The APT37 cyber group, associated with North Korea, has been recognized for carrying out focused attacks by mimicking individuals and distributing harmful HWP files. They pose as writers from broadcasting companies, along with other roles, to create a sense of trust in the target, prompting them to open suspicious emails without hesitation.
As reported by the Genians Security Center on the 22nd, the center has recently uncovered “Operation Artemis” conducted by the APT37 group. Operation Artemis involves cyberattacks where harmful files are embedded within HWP documents.
During the attack phase, spear-phishing was employed to focus on particular individuals or entities by mimicking others. This method was commonly carried out via HWP files. Upon opening the HWP document, the hidden harmful code is triggered, enabling APT37 to infiltrate the user’s system. Throughout this procedure, methods like steganography, which conceals malicious code inside image files, and DLL side-loading, where authentic programs are deceived into loading harmful DLLs as if they were regular ones, were utilized together to mask the execution process and bypass security software.
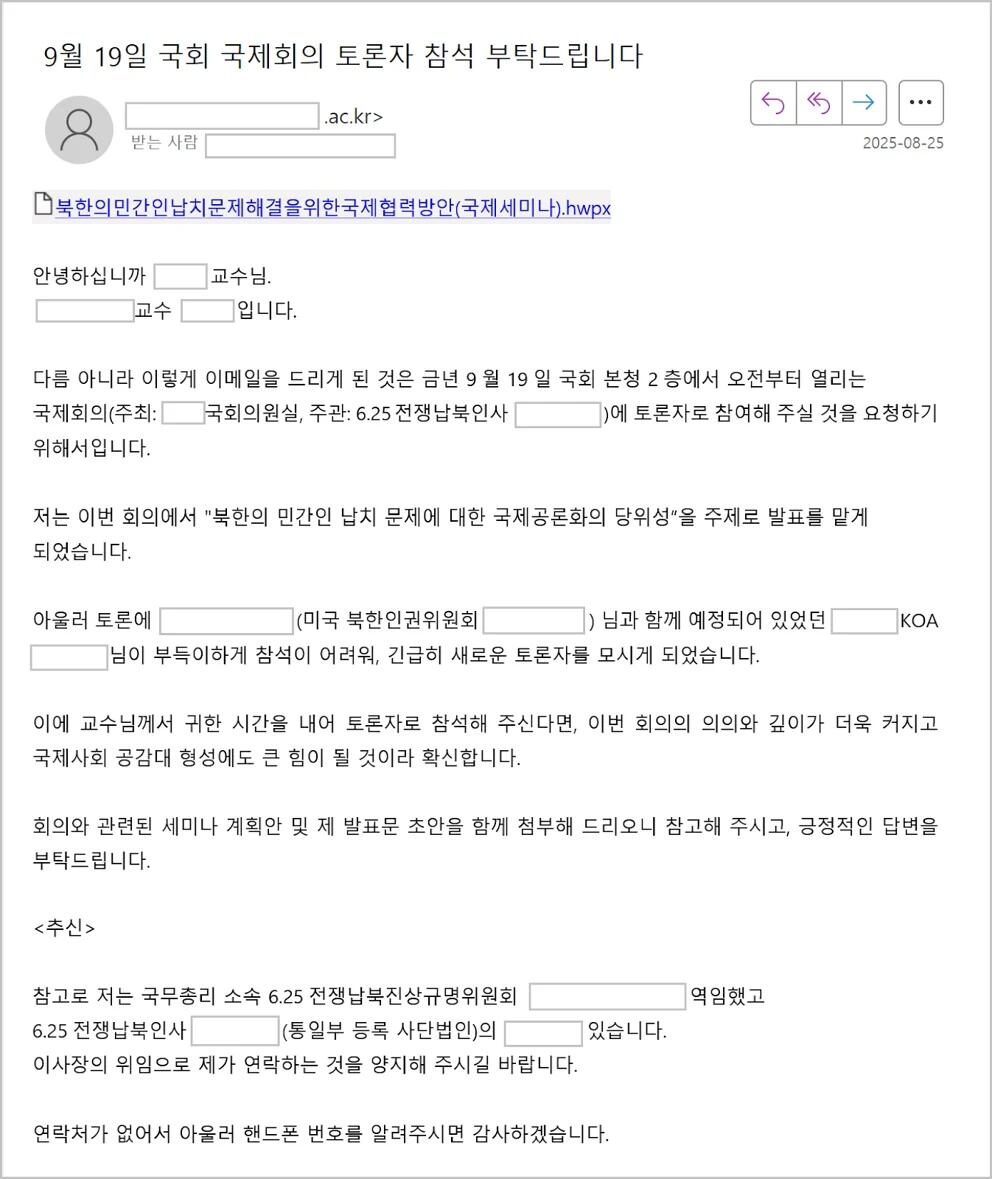
In August of the previous year, an incident occurred where APT37 posed as a particular university professor to invite someone to a discussion and send a harmful file. During that time, APT37 shared a link to an HWP file that could be confused with materials related to the discussion, noting, “Due to unforeseen issues, OO was unable to attend, so we quickly found a new participant.” They managed to avoid suspicion by offering thorough and believable details regarding the discussion’s location, subject, and organizer. This represented a focused deception strategy designed according to the recipient’s area of interest.
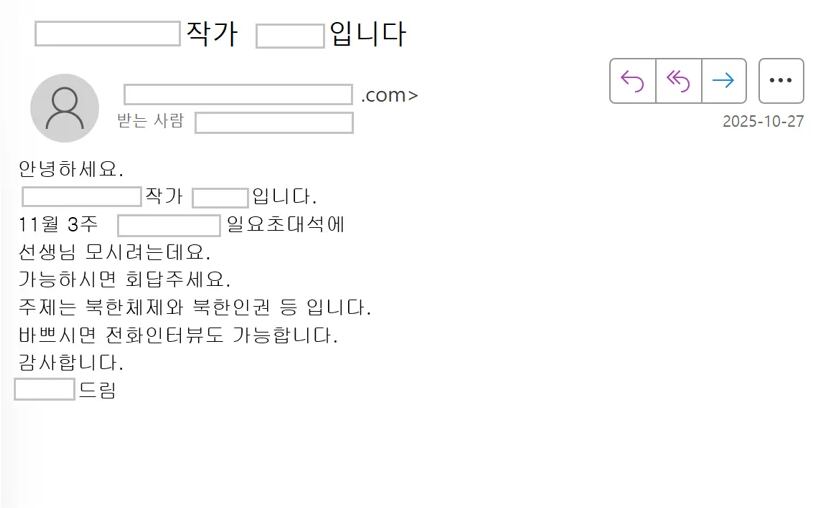
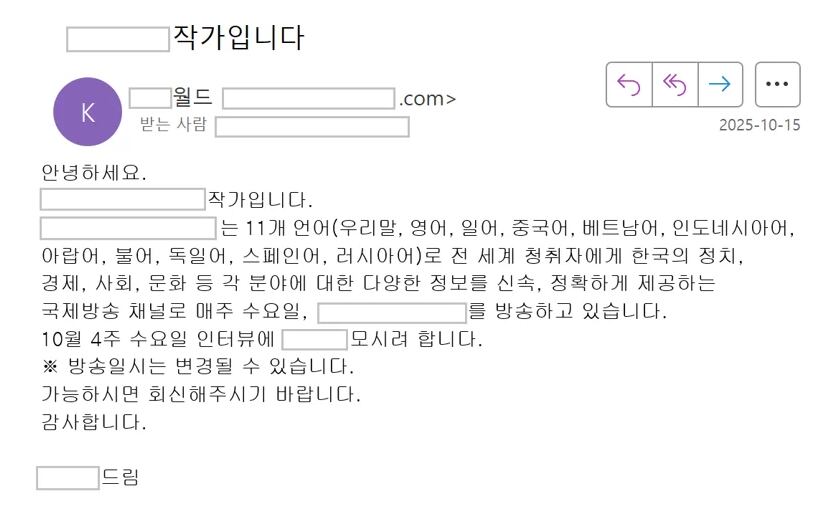
There were instances where they posed as writers for well-known local television programs. They sought interviews concerning the North Korean government and human rights issues, engaged in several trust-building discussions, and subsequently sent harmful HWP files. They specifically encouraged replies by offering thorough details about the broadcast subject and timing. Expressions such as “If you’re busy, a phone interview is also acceptable” were utilized to boost credibility. Rather than sending a file with malicious code immediately, they established trust through regular conversations to raise the chances of the file being opened. This approach was also identified in 2023. At that time, a malicious zip file titled “North Korean Defector Invited Lecture.zip” was shared.
APT37 was observed to have consistently enhanced their cyberattacks over a period of four months, from August to November last year. Significantly, starting in August, they employed steganography techniques using images of people that had not been previously documented.
Genians said, “While APT37’s actions are frequently uncovered in different threat intelligence reports, the instances made public through news articles or certain documents are thought to be just a small part of their real operational scope.” They further noted, “It is highly likely that many hidden operations are being carried out.” They highlighted, “For this reason, ongoing surveillance of activities by prominent state-sponsored threat groups involved in APT attacks and increasing security awareness are crucial.”




Leave a comment